Air-gapped machine monitoring vs. OT network connection - the security case for manufacturers

Every plant manager I talk to faces the same tension: you need data from your machines to reduce downtime and hit OEE targets, but your cybersecurity team, or your own gut, tells you that connecting production equipment to a network is a risk you can't afford. So what do you actually do: keep machines air-gapped and blind, or connect them and hope for the best?
It doesn't have to be an either-or decision. The most practical OT security options for manufacturing in 2025 sit in the middle, and the right approach depends less on ideology and more on how your plant actually runs today.
Key terms before we dive in
These terms get tangled constantly, so let's untangle them once.
Term |
What it means in plain English |
|---|---|
Operational Technology (OT) |
Hardware and software that runs your physical equipment: PLCs, SCADA, DCS, HMIs, sensors |
IT (Information Technology) |
Business systems: ERP, email, office networks |
Air-gapped |
A machine or network with zero connection to external networks, physically or logically isolated |
OT network monitoring |
Watching traffic on your industrial network for anomalies, unauthorized devices, or threats |
Machine condition monitoring |
Tracking equipment health signals like vibration, current, and temperature to predict failures |
ICS / SCADA security |
Protecting the control systems that directly operate your processes |
ISA/IEC 62443 |
The global standard specifically built for industrial automation cybersecurity |
Understanding these distinctions matters because the right security posture depends on which layer you're protecting. Network-level OT security and machine-level condition monitoring are complementary, not competing, capabilities.
The real problem: you can't protect what you can't see
Here's what I keep hearing from operations directors and reliability leaders. You have older machinery, maybe a 25-year-old press or a legacy extruder, running critical production. It has no native connectivity. Your cybersecurity team won't approve an IIoT gateway on the floor because they see it as an attack surface. And meanwhile, you're losing hours every week to unplanned stoppages that nobody fully understands because the data lives in shift-end spreadsheets or operators' heads.
The fear is valid. Manufacturing was the most targeted sector for cyberattacks in 2023, with over a quarter of global incidents hitting manufacturers. Ransomware alone has caused an estimated $17 billion in manufacturing downtime since 2018 (Source: Infosecurity Magazine). The average ransomware-induced shutdown stretches 11.6 days.
But here's the other side of that coin: facilities lose an average of 30 hours per month to unplanned downtime regardless of cyber events. Six in ten manufacturing leaders say these disruptions cost more than $250,000 annually. And 67% of respondents still rely on reactive maintenance approaches.
So the real risk isn't just "someone hacks my PLC." It's that you have zero operational intelligence on equipment that's silently degrading, and you're making maintenance decisions based on calendars instead of conditions.
Why the traditional air gap is breaking down
True air-gapping, where industrial control systems have absolutely no network pathway to external systems, was the default security posture for decades. And in principle, it works: if nothing connects, nothing gets attacked remotely.
In practice, the air gap has been eroding for years. You need remote diagnostics from equipment vendors. Supply chain systems require production data. Multi-plant operations demand standardized reporting. Even air-gapped facilities often have USB drives moving between systems, laptops connecting to PLCs for troubleshooting, or vendor technicians plugging in their own devices (Source: Cyber Defense Magazine).
The question is no longer "should I connect?" but "what's the safest, lowest-risk way to get the data I need?"
The middle path: defense-in-depth with passive, non-intrusive monitoring
The approach that's gaining traction among pragmatic manufacturers is layered security, sometimes called defense-in-depth. Instead of choosing between a sealed vault and an open door, you build multiple layers of protection, each independently valuable.
Here's what that stack looks like in practice:
Layer |
What it does |
Risk to production |
|---|---|---|
Network segmentation |
Divides OT into isolated zones and limits lateral movement if one zone is compromised |
Very low when designed properly |
Passive OT network monitoring |
Watches network traffic without injecting data and flags anomalies or unauthorized devices |
Zero: no additional traffic or latency |
Controlled access gates |
Time-bound, auditable vendor access that auto-revokes after maintenance windows |
Low |
Non-intrusive sensor monitoring |
Clip-on current sensors on power lines that read a machine's heartbeat without touching controls |
Zero: no PLC integration required |
Condition-based alerts |
Algorithmic analysis of sensor data to predict failures |
Zero: analysis happens off the control path |
The key point for any team whose cybersecurity group won't approve an IIoT gateway on the floor: non-intrusive sensor-based monitoring doesn't touch your OT network at all. A clip-on current sensor reads the electrical signature of a motor through electromagnetic induction. It connects to its own data pathway, often cellular, completely bypassing the plant network. Your PLCs never know it's there.
Non-intrusive clip-on current sensors offer a way to gain machine-level visibility without any PLC integration or OT network access. They use independent cellular connectivity, meaning your cybersecurity team doesn't need to approve network changes, and deployment on critical equipment can happen in days with zero production downtime. This approach lets you start collecting actionable data immediately while longer-term network segmentation and passive OT monitoring initiatives proceed in parallel.
This is how platforms like Guidewheel work: simple clip-on sensors read current from any machine, legacy or new, and transmit data via cellular connection without requiring IT network access. The algorithms that process these current signals turn raw electrical patterns into run/down states, cycle counts, and anomaly detection.
Where the downtime actually hides
So what does the data say once you finally get it? Performance analysis across 3,000+ machines reveals that the actionable downtime, the kind your team can actually fix, spans several categories that deserve equal attention (Source: Guidewheel Performance Analysis).
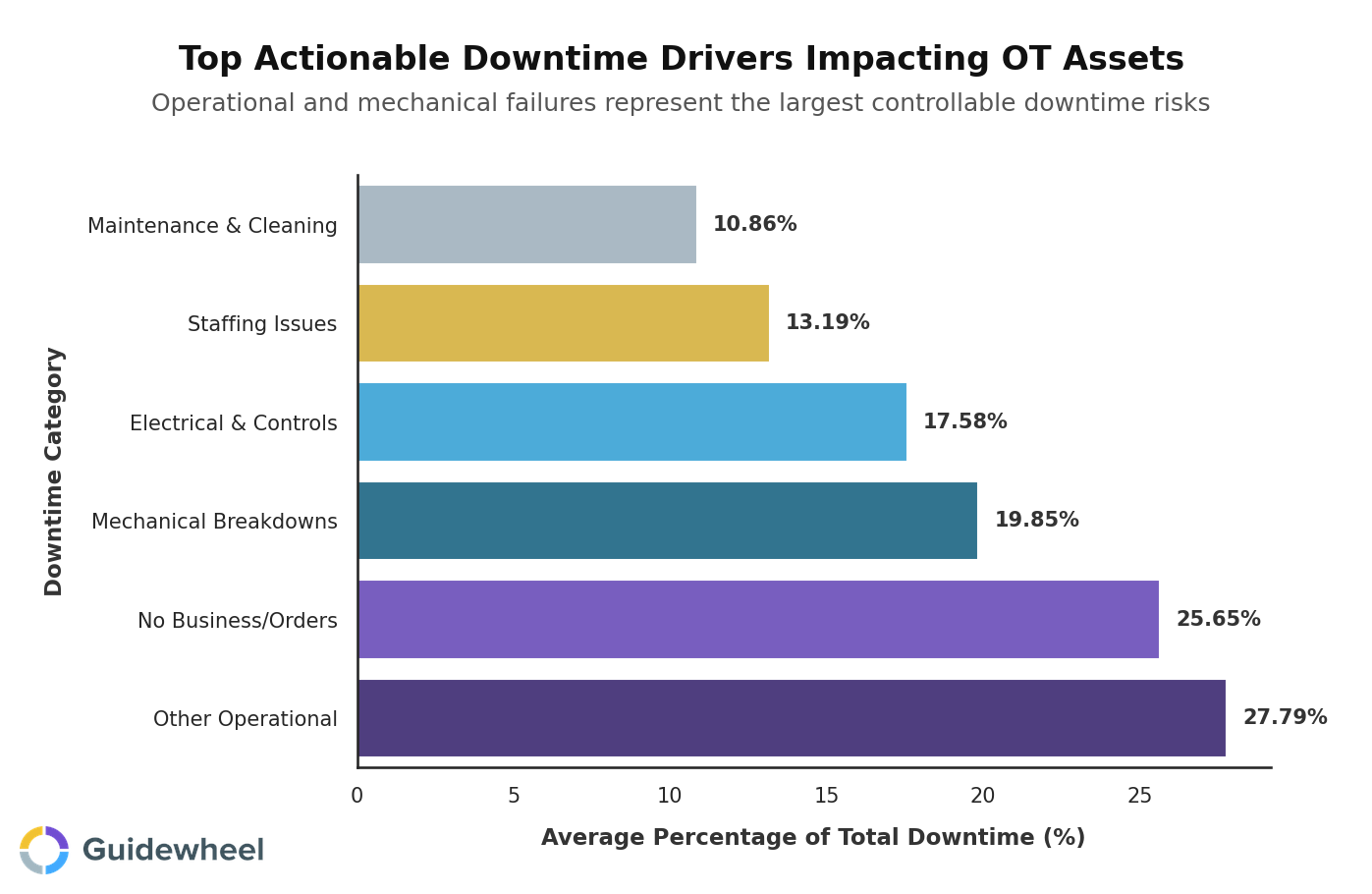
While market-driven downtime, or no orders, creates the longest individual events at 318 minutes average, the categories your team controls paint a clearer picture of improvement opportunity:
Downtime category |
% of total downtime |
Avg. minutes per event |
Industries affected |
|---|---|---|---|
Other Operational |
28% |
81 |
11 |
Mechanical Breakdowns |
20% |
72 |
11 |
Electrical & Controls |
18% |
107 |
7 |
Staffing Issues |
13% |
197 |
7 |
Maintenance & Cleaning |
11% |
85 |
8 |
Mechanical breakdowns and electrical/controls failures are exactly the failure modes that machine condition monitoring software is designed to catch early. When you're tracking current signatures, vibration patterns, and temperature trends continuously, you spot degradation weeks before catastrophic failure. A bearing developing subsurface fatigue produces subtle current-draw changes long before it seizes.
Electrical and controls issues, averaging 107 minutes per event, are directly relevant to OT network health. These are often the hardest to troubleshoot without data because intermittent faults don't leave obvious evidence. Continuous monitoring captures what shift-end reports miss.
Keep in mind that these benchmarks serve as reference points. Every facility has unique equipment, materials, and production goals that influence what good looks like for their operation.
The utilization gap most plants don't know they have
Here's something that surprises almost every operations director I work with. The gap between what high-volume machines achieve and what the median machine actually runs is enormous, even within the same industry.
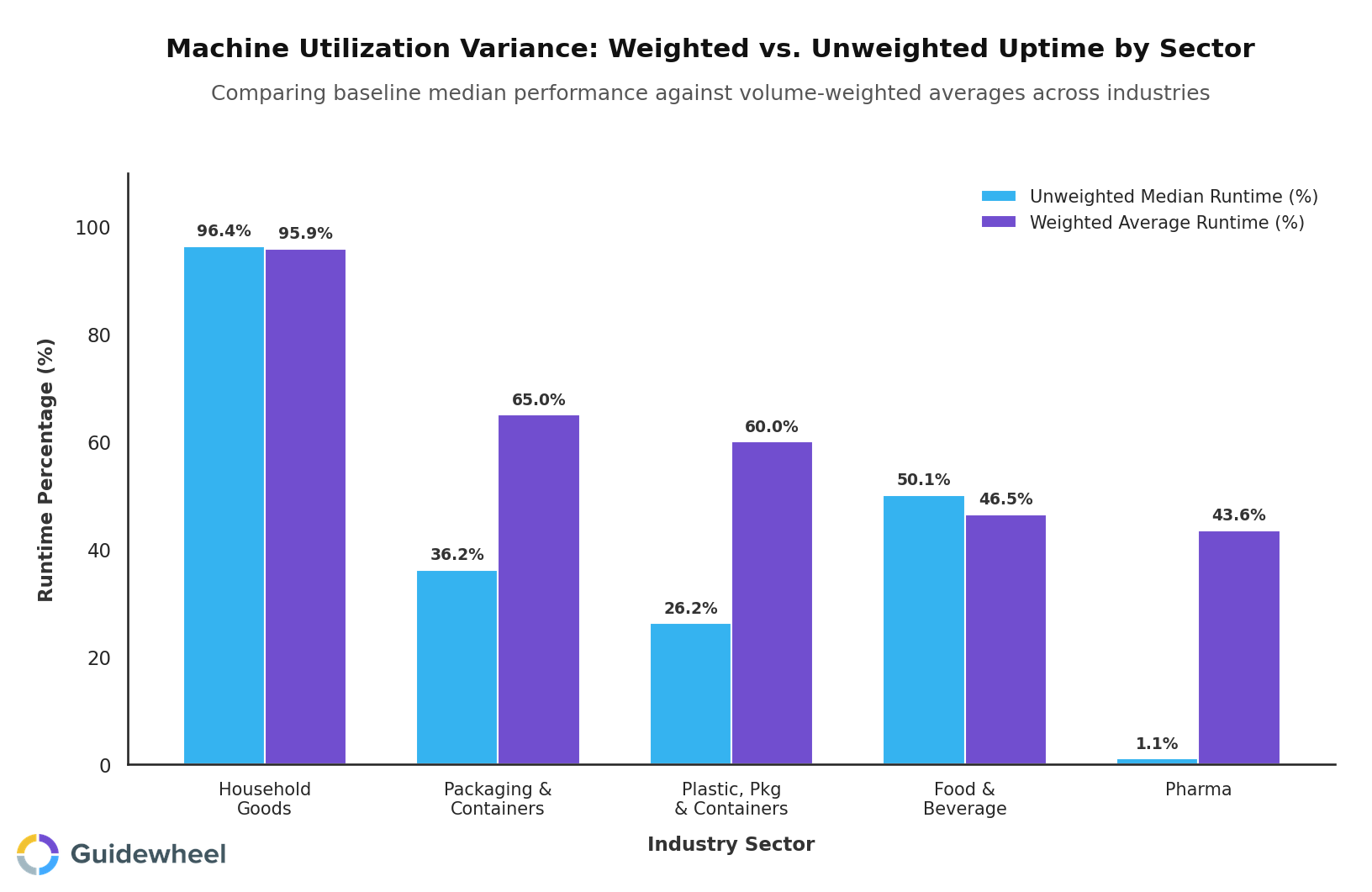
In plastics, the weighted average runtime is 60%, but the median machine runs only 26% of the time. In pharmaceuticals, the spread is even wider: 44% weighted average versus a 1% median. That variance means a small number of well-monitored, well-maintained machines carry most of the production load while the rest operate far below potential.
Without machine-level visibility, you can't see this gap. Your top-performing machines mask the underperformers in aggregate reports. Building a security case for connectivity starts with showing leadership that the cost of blindness, measured in hidden capacity and preventable downtime, exceeds the risk of carefully controlled data collection.
A practical implementation playbook
If you're building a business case for machine-level monitoring that sidesteps OT network concerns, here's a phased approach that works:
Week 1-2: Deploy non-intrusive sensors on your top 5-10 critical machines. Clip-on current sensors require no PLC access, no network integration, and no production downtime to install. Use cellular connectivity to bypass IT entirely.
Week 3-4: Establish baselines. Let the system learn normal operating patterns for each machine. Algorithms identify cycle times, run/idle/down states, and typical current signatures automatically.
Week 5-8: Activate downtime tracking and alerts. Operators begin categorizing stops. Pareto analysis surfaces your top loss drivers. Proactive alerts notify maintenance when anomalies emerge.
Month 3+: Expand to secondary assets and integrate condition-based maintenance triggers. Replace calendar-based PM schedules with data-driven intervals for monitored equipment.
Ongoing: Layer in OT network segmentation and passive network monitoring as a parallel security initiative. The machine-level data from sensors and the network-level data from passive monitors become complementary sources of truth.
This phased approach delivers ROI fast. Industry data indicates that facilities implementing predictive maintenance achieve 32% downtime reduction on average, with payback periods of 9-14 months. Planned interventions cost 60-75% less than emergency repairs.
Start with the data, then secure the architecture
The security case for manufacturers isn't about choosing air-gapped isolation or full network connectivity. It's about finding the lowest-risk path to the operational intelligence your team needs. Non-intrusive, sensor-based machine monitoring that operates independently of your OT network gives you that intelligence without creating the attack surface your cybersecurity team rightly worries about. From there, you can layer in network segmentation, passive OT monitoring, and controlled access as your security maturity grows.
The manufacturers winning right now are the ones who stopped debating connect or don't connect and started asking, what's the safest way to get the data we need to prevent the next unplanned shutdown?
Ready to see what your machines are actually doing? Book a Demo and get sensors on your critical equipment in days, not months, with zero IT burden.
We had our best month of the year, increasing production from 26k-35k/month to 46k cases in March. I attribute this to Guidewheel. Being able to see downtime data and address downtime reasons directly correlates to higher production.
Michael Palmer, VP of Operations, Direct Pack via Guidewheel's Customer Research
Frequently asked questions
Is air-gapped monitoring really safer than connecting to the OT network?
In theory, a fully air-gapped system eliminates remote cyber risk. In practice, true air gaps are rare in modern manufacturing because vendor access, USB transfers, and diagnostic connections create hidden pathways. A more practical approach uses non-intrusive sensors with independent cellular connectivity, giving you machine data without touching the OT network at all. This delivers the safety benefits of isolation while eliminating the operational blindness that pure air-gapping creates.
What security risks come with connecting machines to Wi-Fi or plant networks?
Any device added to your OT network becomes a potential entry point for lateral movement if the network is compromised. Risks include unauthorized device discovery, man-in-the-middle attacks on unencrypted industrial protocols, and expanded attack surface for ransomware. Network segmentation following the Purdue Model and passive OT network monitoring significantly mitigate these risks by isolating critical control systems and flagging anomalous traffic before it reaches production equipment.
How does machine condition monitoring software fit into an OT security strategy?
Machine condition monitoring and OT security share a common foundation: knowing what assets you have and what normal looks like. Condition monitoring tracks equipment health signals like current draw, vibration, and temperature to predict failures. OT security monitoring tracks network behavior to detect threats. Together they create a complete picture, covering both equipment degradation and cyber anomalies, without requiring a single monolithic platform.
What KPIs should plants track to connect OT monitoring to operational performance?
Focus on metrics that translate directly to business outcomes: unplanned downtime hours prevented measured against a historical baseline, maintenance cost reduction broken down by labor, parts, and contractor spend, OEE improvement by shift or line, mean time to detect and resolve equipment issues, and prediction accuracy rates as your system learns your equipment. Quarterly review cycles give you enough data to spot trends without creating noise from week-to-week variability.
How do I build a business case for monitoring that doesn't require OT network access?
Start with the cost of your current blind spots. Calculate your monthly unplanned downtime hours, multiply by your hourly production value, and that's your baseline cost of not having data. Then compare it against a sensor-based approach that uses cellular connectivity, requires no IT integration, and deploys in days. Show that the monitoring investment pays for itself through prevented downtime alone, typically within the first year, and you avoid the lengthy cybersecurity approval process entirely.
About the author
Lauren Dunford is the CEO and Co-Founder of Guidewheel, a FactoryOps platform that empowers factories to reach a sustainable peak of performance. A graduate of Stanford, she is a JOURNEY Fellow and World Economic Forum Tech Pioneer. Watch her TED Talk—the future isn't just coded, it's built.

